Cybermap: From Labs to Live Incidents
From controlled lab environments to real production incidents, this page showcases practical security analysis, attacker behavior, and defensive response in action.

- Incident
- Security
- WordPress
The WordPress Security Incident that started as spam & led to the discovery of a full site compromise: Incident response in a real-world scenario.
- Phishing
- Lab
- Threat Detection
My Step-by-step analysis of a phishing attack, from email delivery to credential theft and network-level evidence.
- PHP
- SQL
- DB
- JS
- CSS
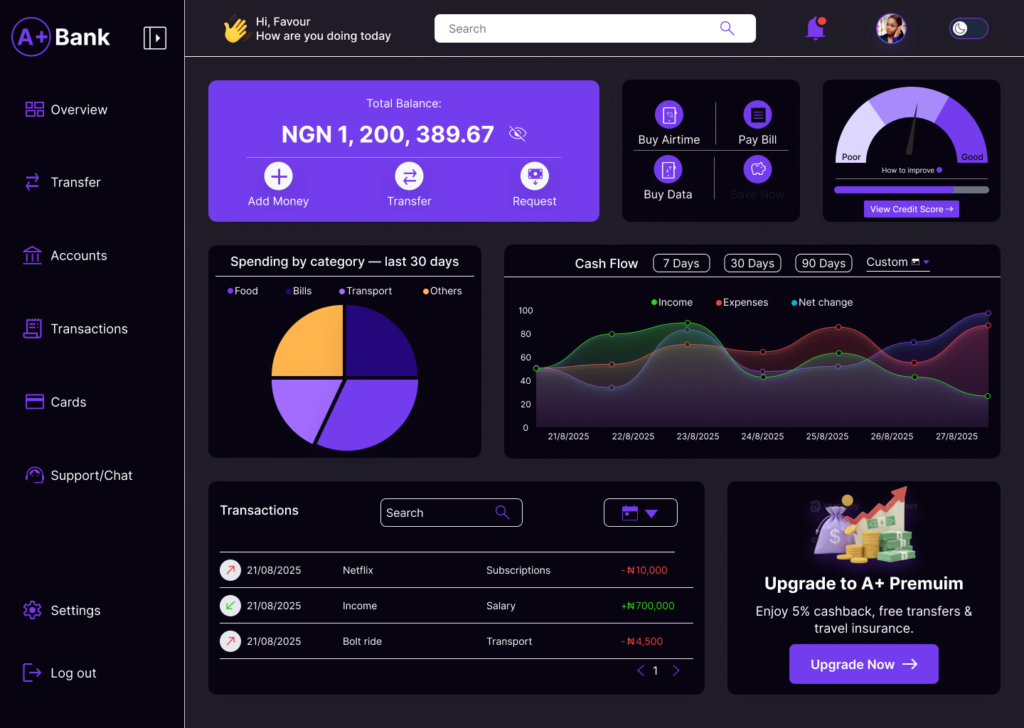
It includes a robust user registration and login system with access control.
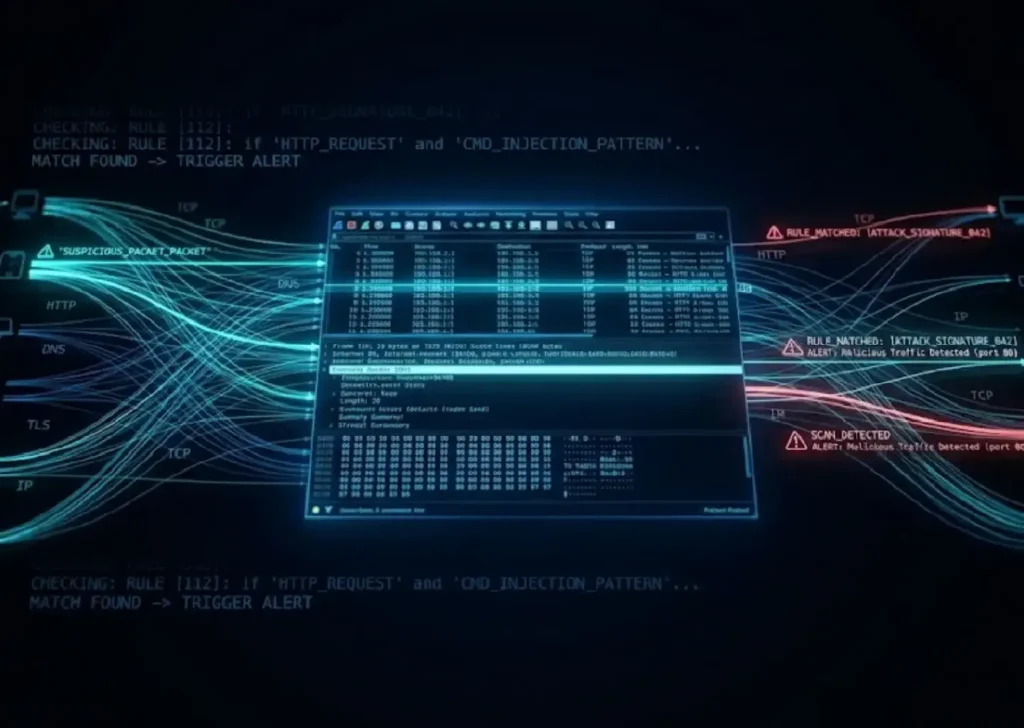
- Network Attack
- Snort
- Log4Shell
How to detect real-world network attacks using Wireshark and Snort, including Log4Shell, HTTP analysis, and custom IDS rule creation.
- AI
- API
- JS
Inspire and be inspired with a click of a button, and meditate on a new quote.
- Azure
- SIEM
- Log
- PowerShell
This project documents the design and implementation of a personal blue-team detection lab using Windows telemetry and cloud-native SIEM monitoring.

- Network
- Wireshark
- ARP Scan
Hands-on network traffic analysis Lab, learned how to detect ARP scans, DNS tunneling, and data exfiltration using Wireshark with real examples.
- UI/UX
- Figma
- UI/UX
- WordPress
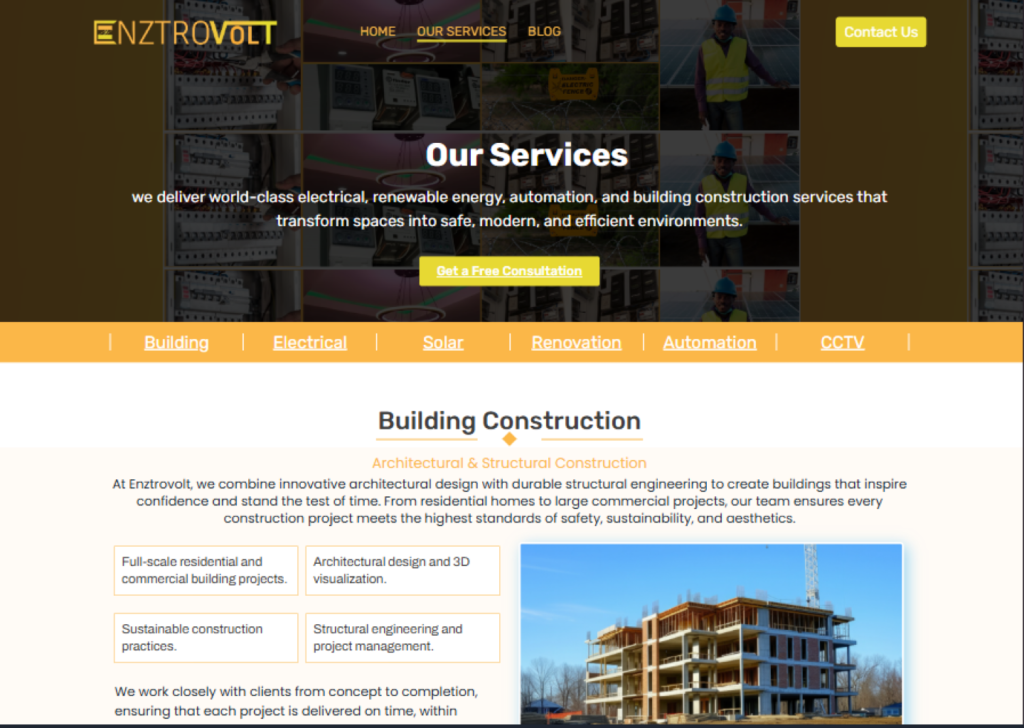
Enztrovolt is designed to highlight expertise and attract potential clients.

